A User-Agent is a part of the header of an HTTP request that contains information about the user agent program that is sending the request, typically used to identify the client software, operating system, device type, browser type and version, etc. that is sending the request.
What Information is Contained in a User-Agent String?
The User Agent string consists of several parts, each of which contains specific information.
For example, the User Agent string for a particular browser might look like this:
Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/125.0.6422.60 Safari/537.36
- Mozilla/5.0: This is a generic logo that was originally used for the Mozilla browser and is now included in almost all browsers to indicate that they are Mozilla compatible.
- Windows NT 10.0: Indicates that the user’s operating system is Windows 10. “Windows NT” was the name of Microsoft’s early operating system, and modern versions of Windows carry that name.” 10.0″ is the internal version number of Windows 10.
- Win64; x64: Indicates that the user’s system architecture is 64-bit.” Win64″ indicates a 64-bit version of Windows, while “x64″ refers to a 64-bit processor architecture.
- AppleWebKit/537.36: AppleWebKit is the browser’s rendering engine, which is responsible for parsing web page code and displaying it as visual content.” 537.36″ is the specific version number.
- (KHTML, like Gecko): KHTML is an open source rendering engine, and “like Gecko” means that the browser is compatible with the features of the Gecko rendering engine, which is the rendering engine of the Mozilla project.
- Chrome/125.0.6422.60: Indicates that the user is using Google Chrome, version 125.0.6422.60.
- Safari/537.36: indicates that the browser is compatible with certain features of the Safari browser.” 537.36″ matches the version number of AppleWebKit.
How Does User-Agent Leak Browser Information?
1. Tracking User Behavior: Many websites use User-Agent to track user’s browser information in order to collect data about the user’s device, preferences, and behavior. This information can be used for customized advertisements, personalized recommendations, and more.
2. Identifying Browser Vulnerabilities: Malicious websites or hackers can use User-Agent to determine which browser and operating system version a user is using in order to attempt to target known vulnerabilities.
3. Browser Fingerprinting Technology: With information such as User-Agent, websites can create unique browser fingerprints that can be used to identify and track users, even if they have cleared their browser cookies.
How to Minimize User-Agent Leakage of Browser Information?
1. Use Private Browsing Mode: Private Browsing Mode can reduce the amount of personal information exposed by User-Agent.
2. Limit Cookie Sharing: Limiting the use of third-party cookies in your browser settings can reduce the ability of websites to track users.
3. Disable JavaScript: JavaScript can capture User-Agent information, so disabling JavaScript may help reduce the risk of information leakage.
4. Change User-Agent and disguise UA information: The most thorough method is to modify UA information to disguise another UA, and fingerprint browsers can modify and disguise UA information. VMLogin Antidetect Browser, which can modify UA information such as OS and version, language, browser name/version/engine, and device type (tablet or cell phone) to form a new User-Agent, which prevents leakage of real UA information. If you need to run multiple businesses or accounts on a single device, then changing the UA is critical.
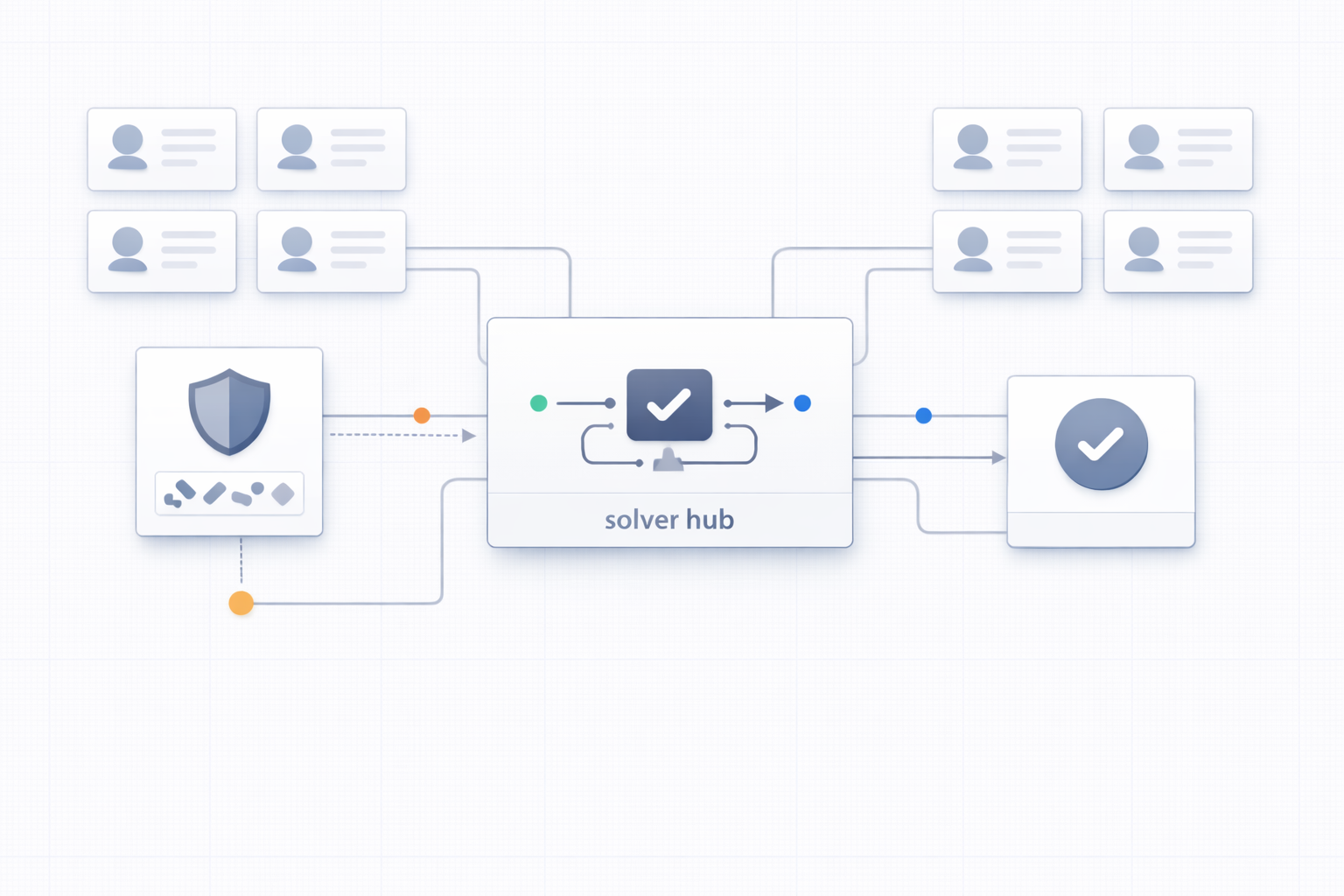
VMLogin generates a fingerprint that matches the real device and provides a unique environment for different accounts, which keeps them private and secure.
New users can try it for three days!