In the present world, security threats are becoming more and more familiar to organizations. Below are some security threats that virtual browsers aim to combat.
What Browser Security Threats Do Virtual Browsers Deal With?
Internet security is very crucial to organizations as well as individuals alike. There must be a barrier between harmful online content and the end user. Browser privacy is an essential component of browser security. Most of the popular browsers, needless to be named, sell the end-user data to third parties, including advertisers.
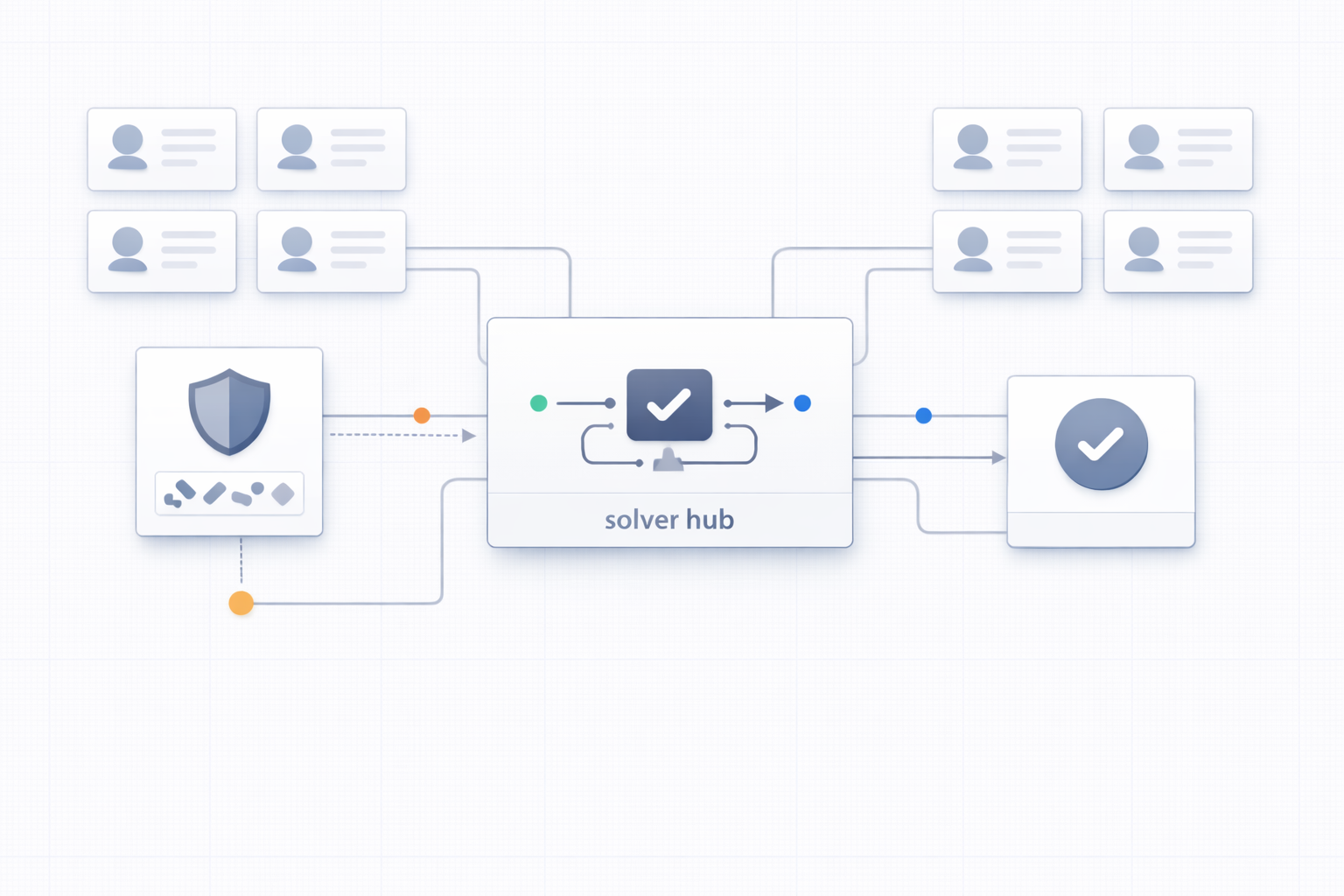
Virtual browser act as a shield between the browser and the end-user. It prevents sharing of usernames, passwords, and other critical information that could be a potential target of hackers online. In the absence of a virtual browser, the data is usually stored in cookies, which the browser providers can further sell. Let’s discuss some other security threats you might be experiencing right now!
Defining Browser Security
The web browser has come a long way, from showcasing text documents to engaging with a wide variety of content online, including dynamic web applications and rich media. Although it’s impressive for a single platform to provide all such media types and functions, there’s a huge price the end-users have to pay.
The web browser’s complexity brings out certain weaknesses that give way for a hacker to exploit. A list of the most common weaknesses of the browser includes weak antivirus, unblocked popups, unsafe plugins, malicious redirects, malicious browser extensions, use of saved passwords, and DNS attacks.
Top Browser Security Threats
Below mentioned are some of the most alarming browser security threats by popular browsers that online virtual browsers aim to combat.
1. Extensions & Plugins
Browser extensions and plugins are usually used to improve website functionality and user experience. Even though certain plugins are professionally made, some of them are flawed and have a crack open to welcome vulnerabilities and security issues. At times, such plugins are created deliberately, having malicious intent.
It’s wise to create policies that restrict the end-user from installing extensions and plugins, as it’ll ultimately prevent threats of this kind. You can customize it to allow certain plugins and restrict others.
2. Saved Passwords and Others
Passwords are meant to safeguard critical information and restrict access to networks & systems. In case swindlers get their hands on passwords, they can very well use them to gain illegal access to databases, networks, and systems. The problem lies in the weak and short passwords that users create for their accounts. Further, they use the browser to save passwords for future use.
It’s essential to raise awareness among users not to save passwords in their browsers. Instead, disable the feature if possible. Do you know what’s even better? Make the most out of the availability of virtual browsers online. Organizations can either take a subscription or use it in all their systems.
3. Weak Antivirus
Attackers have devised incredibly genuine ways to break through antivirus software or other protection measures. Unfortunately, most of them manage to pass through the antivirus program undetected. Therefore, deploying virtual browsing platforms is strongly recommended. It creates a shield between your critical data and external threats online.
Speaking of organizations, it’s their responsibility to ensure operating systems, browsers, and other software are running in their most secure and updated version. Employee training is important to raise awareness about phishing and other types of web attacks.
4. DNS Servers
Once you enter an address in the web browser, it connects directly to a DNS server to find a matching IP address of the address entered. It’s the DNR server that directs the browser to a suitable website. However, there are high chances that attackers can intrude into the connection and subvert it in a lot of ways. For instance, they can wrongfully direct you to a malicious site.
To keep the DNS server untouched from attackers, organizations are recommended to use a virtual browser online to conceal critical information about the server. It sets strong security measures and compliance terms.
5. Pop-up Ads and Redirects
Popups are used as a weapon by attackers to deploy malicious codes into computers. It might coerce users to download malware or access insecure websites. The attackers’ tactics include flashing a popup that won’t close or giving false warnings and fooling them into downloading a malware-packed program.
Yet another popular tactic used is malware-rich redirects. In this process, the user is misdirected from a safe page to an insecure page. The infected page could proclaim a warning or a threat to fool visitors into downloading malware, utilize browser or operating system vulnerabilities to trigger a drive-by download, or it might pose as a legit page to seek the user’s private information.
Conclusion
All the threats mentioned above have the capability to cause harm beyond your imagination. You never know who’s keeping track of what information about you. So, always equip your systems with a virtual browser to make a shield between the hungry attackers and your crucial information. Its multi-layered detection mechanism will prevent the threat of ransomware, APTs, malware, phishing, and more.
Have you been looking to secure a virtual browser online free trial? VMLOGIN is the halt to your search! From a separate browsing environment to fingerprint protection, and easy browser automation, it’s equipped with all the features to ease your work while ensuring safety! Plus, to further build your trust, we offer a 3-day free trial. Try us out before taking the subscription. For further queries, write to us at [email protected] or check out our website.